Remote authentication framework (TUBA)
Summary:
Key loggers are a form of malware (bots) that eavesdrop on users to steal keystroke sequences that can then be used to hack individual’s identity. This form of malware enables the capture of user ids, passwords, credit card numbers, bank accounts and pins – causing personal, governmental, military and enterprises harm. Determining whether a computer is infected or not can be very challenging. Malicious bots are stealthy and difficult to detect using conventional anti-virus Software. Some bots even disable the anti-virus software immediately after they successfully infect a machine.
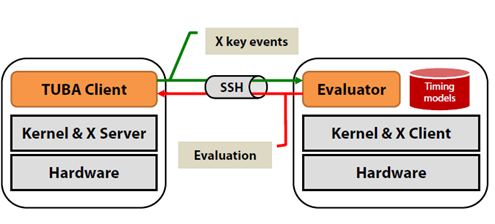
Researchers at Rutgers University and Virginia Tech have developed technology to proactively distinguish human input events (e.g., keystrokes) from those generated by botnet malware. Our technology uses characteristic behaviors of humans when entering keystrokes (e.g., keystroke dynamics), instead of the patterns of the malware during operation used in most existing solutions. In addition, our solution uses machine learning, artificial intelligence (AI) technology to distinguish characteristic usage patterns of users operating the computer from ones generated by malware.
Unlike conventional malware solutions which are reactive, requiring updates, patches, and downloads; our technology is always available and does not require updates or patches to operate.
Advantages:
- Provides security protection that is robust, pro-active, and accurately detects infected computers.
- Defends against new exploits and attacks without the need for security updates and patches.
- Faster than existing technologies which require creation and extraction of signatures when faced with new and emerging attacks.
- Enables personalized security using AI that is customized for individuals; making it difficult for attackers to break or circumvent
- Uses "keystroke dynamics” an inexpensive biometric mechanism that has been proven accurate in distinguishing individuals"
Market Applications:
- Desktop and server computer security solutions including ones for: Threat Detection, Endpoint Security, Malware detection, Malicious keyloggers, Anti-phishing solutions
Intellectual Property & Development Status:
US8763127, US9888030; Available for licensing.